
CSO Perspectives Roadshow Sydney
Sydney's CSO Perspectives Roadshow was a place for sharing of unique challenges, including awareness and preparedness, amongst Sydneys elite IT Security community.
13 Nov | View galleries

Sydney's CSO Perspectives Roadshow was a place for sharing of unique challenges, including awareness and preparedness, amongst Sydneys elite IT Security community.
13 Nov | View galleries

CSO Perspectives Roadshow infiltrates Canberra security community
08 Nov | View galleries

In the spirit of Halloween, CSO recently spoke to Adam Stewart, the Vice-President of Engineering at Autotask, to outline the most frightening aspects of working in IT.
30 Oct | View galleries

The Identity Theft Resource Center has recorded 450 data breaches so far this year, and here are the worst that become known between July and September
15 Oct | View galleries

Facebook has changed its privacy and security settings often enough that most users now have no idea what settings they actually need
03 Oct | View galleries

The headlines may be filled with cyber-attacks and government-level efforts to boost IT security, but for the average CIO, 2013’s security challenges revolve around the myriad threats posed by ever more powerful business agendas. The explosion in demand for bring-your-own-device (BYOD) policies and the maturation of cloud computing, in particular, are escalating IT security to the highest levels of the executive.
17 Sep | View galleries

Passwords are a security weak link, but these products help shield passwords from attackers
09 Sep | View galleries

Symantec Australia held its annual symposium at the Sydney convention centre. Delegates heard insights from Symantec's Brenton Smith, Sean Kopelke and Fujitsu’s John Kaleski.
05 Sep | View galleries

CSO Trend Micro Workshop
30 Aug | View galleries

Here are 10 companies and why they have a shot at challenging Amazon.
27 Aug | View galleries

After breaking into networks for fun, profit, and to fulfill political agendas, some did prison time.
15 Aug | View galleries

IP theft continues to be a threat to businesses’ bottom lines – and a major issue for Sino-American relations.
14 Aug | View galleries
Everyone seems to be jumping on the bring-your-own-device (BYOD) bandwagon, but it's a bumpy ride. There are many ways to fall off and get a bloody nose (or worse). As the BYOD reality catches up to the hype, here are 12 very real disaster scenarios.
06 Aug | View galleries

Which tech newsmakers have made the biggest splash so far this year, and which have gone splat?
06 Aug | View galleries

From an Edward Snowden cutout to panties with a message the premier security conference has it all
03 Aug | View galleries
The annual Security exhibition and conference took place in Sydney during July. Delegates heard from the Bank of England, NBN Co and terrorist expert Doctor Anne Speckhard.
29 Jul | View galleries

Check Point wins test of eight unified threat management (UTM) devices for small business.
25 Jul | View galleries

We list the worst data breach incidents recorded by ITRC
19 Jul | View galleries

Can hackers, stalkers, criminals, and other Internet users track you down by your Internet Protocol (IP) address?
17 Jul | View galleries
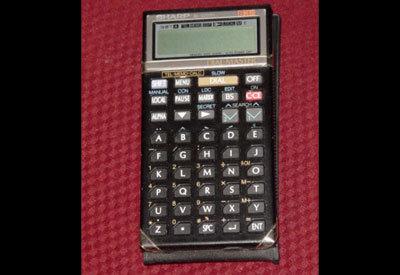
Still got an old Blackberry or Compaq laying around? CSO Publisher (and packrat) Bob Bragdon does! Rummaging around Bragdon's attic (with some memory help from mobile office expert Catherine Roseberry) provides a look at how mobile device security has evolved.
09 Jul | View galleries